Know what you're buying before you sign.
AI-driven codebase evaluation you can trust.
You're about to sign a vendor contract. Or acquire a company. Or bet your product roadmap on a third-party codebase. The demo looked great. The pitch was polished. But what's actually under the hood? If you're also evaluating AI governance policies, Shield provides the technical due diligence to complement your policy framework.
Most companies find out too late. Phoenix AI Solutions runs deep security audits before you commit.
What Shield Does
Evidence-based codebase evaluation so you make decisions based on facts, not demos. Found critical issues? Custom AI Solutions can rebuild problem areas identified by Shield.
Codebase Quality Assessment
Deep analysis of code architecture, patterns, and practices. Is this codebase maintainable, or is it held together with duct tape?
Security Risk Analysis
Identify vulnerabilities, dependency risks, and exposure points before they become incidents. Need governance frameworks? Pair with AI Policy for complete compliance.
Technical Debt Mapping
Quantify the true cost of inheriting or integrating this code. Know what you're really paying for.
Vendor Validation
Cut through the demo theater. Shield evaluates whether a vendor's technology actually does what they claim.
Who It's For
CTOs, VPs of Engineering, and technical due diligence teams who need the truth before making a decision.
The Phoenix Difference
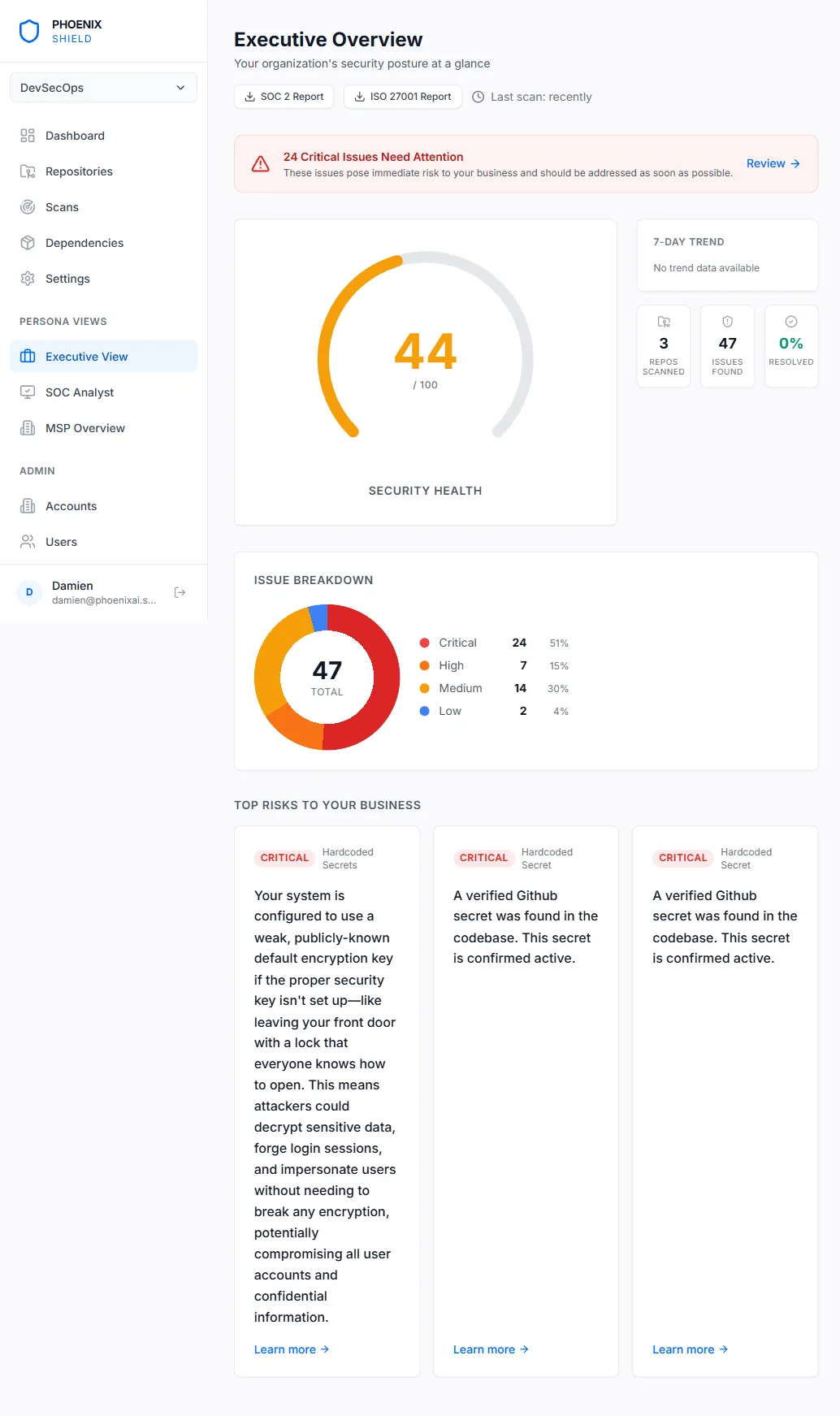
Most security tools give you a list of problems and leave you to figure it out. Phoenix Shield finds the issues, verifies they're real, generates the fix, and opens the PR.
- AI-verified findings — false positives filtered automatically
- Auto-generated patches with GitHub PR creation
- Health Score that executives actually understand
- Five engines in one platform — no tool sprawl
- Full finding lifecycle from detection to verified fix
What you get:
- Codebase quality assessment
- Security risk analysis
- Technical debt mapping
- Vendor validation
- AI code analysis + Semgrep SAST + TruffleHog secrets + Trivy SCA
- Automated patch generation and GitHub PR creation
Real Phoenix Shield Assessments
Phoenix Shield delivers measurable risk reduction and cost savings in pre-acquisition due diligence, compliance prep, and security audits. Here are three verified assessments.
The Challenge
Due diligence phase before acquisition. Vendor claimed "enterprise-grade security" but provided no evidence. PE firm needed independent codebase assessment before signing. Timeline: 2 weeks to complete technical due diligence or deal at risk.
The Solution
Phoenix Shield rapid assessment: scanned 78,000 lines of code across 3 repos, identified security vulnerabilities and technical debt, generated executive summary for board, provided remediation cost estimates.
Measured Results
- 12 critical security vulnerabilities discovered (vendor unaware of 9)
- 3 hardcoded API keys with production access (immediate security risk)
- 34% of dependencies outdated with known CVEs
- Technical debt estimated at £180K to remediate (not disclosed by vendor)
- PE firm renegotiated purchase price down £325K based on Shield findings
- Post-acquisition: used Shield-generated patches to fix critical issues in 3 weeks
The Challenge
Lead investor required security audit before finalizing investment. Internal team had no security expertise. Needed clean audit to close round within 4 weeks. Previous startup in portfolio had post-investment security incident that cost £450K to remediate.
The Solution
Phoenix Shield pre-investment security assessment: full codebase scan (42,000 lines), dependency vulnerability analysis, secrets detection, AI-verified findings with auto-generated patches, investor-ready security report.
Measured Results
- 8 high-severity vulnerabilities identified and patched before investor audit
- Zero critical findings in investor security review (passed with no issues)
- £3.5M funding round closed on schedule
- Avoided post-investment security remediation costs (estimated £85K-£180K)
- Established ongoing Shield monitoring for continuous security assurance
- Investor quoted Shield report in board materials as evidence of technical diligence
The Challenge
Rapid growth with legacy code written 6 years ago by outsourced team. New CTO discovered no security audits had ever been conducted. PCI DSS compliance audit upcoming in 8 weeks. Risk of non-compliance, customer data breach, and regulatory fines up to £1.8M.
The Solution
Phoenix Shield comprehensive security audit: scanned 185,000 lines across monolith and 12 microservices, identified PCI DSS compliance gaps, generated prioritized remediation roadmap, created patches for critical findings.
Measured Results
- 22 critical vulnerabilities patched before PCI audit (11 would have failed compliance)
- SQL injection vulnerabilities in payment processing flow eliminated
- Insecure session management fixed (customer account takeover risk)
- PCI DSS compliance audit passed with zero security findings
- Avoided estimated £1.8M regulatory fines for non-compliance
- Ongoing Shield monitoring deployed (monthly scans, continuous compliance)
Phoenix Shield Assessment Methodology
Our proprietary framework combining automated scanning, AI verification, and expert review to deliver accurate, actionable security findings in days, not weeks.
Phase 1: Automated Multi-Engine Scanning (Hours)
Five security engines scan your codebase in parallel: SAST, SCA, secrets detection, code quality analysis, and architecture review. Comprehensive coverage in hours, not weeks.
- SAST (Static Application Security Testing): scans for vulnerabilities like SQL injection, XSS, authentication flaws
- SCA (Software Composition Analysis): identifies outdated dependencies and known CVEs
- Secrets detection: finds hardcoded API keys, passwords, tokens, and credentials
- Code quality analysis: evaluates maintainability, technical debt, and anti-patterns
- Architecture review: assesses overall system design, integration points, and risk hotspots
Phase 2: AI Verification & Prioritization (24-48 Hours)
AI analyzes scan results to eliminate false positives, verify exploitability, and prioritize by business impact. Reduces noise by 95%.
- False positive filtering: AI verifies findings against code context and removes false alarms
- Exploitability analysis: determines if vulnerability is actually exploitable in your architecture
- Business impact scoring: ranks findings by potential damage (data breach, compliance, availability)
- Dependency chain analysis: maps vulnerable dependencies to actual usage in your code
- Fix complexity estimation: predicts effort required to remediate each finding
Phase 3: Auto-Patch Generation (24-48 Hours)
For verified vulnerabilities, AI generates fix code tailored to your codebase. Delivered as GitHub pull requests ready for review and merge.
- Context-aware patches: fixes account for your coding style, frameworks, and architecture
- Dependency updates: automatic version bumps with compatibility checks
- Security best practices: patches follow OWASP guidelines and industry standards
- Testing validation: patches include tests to verify fixes don't break functionality
- GitHub PR creation: patches delivered as pull requests with detailed explanations
Phase 4: Expert Review & Reporting (2-5 Days)
Human security experts review AI findings, validate critical issues, and prepare executive and technical reports. You get both board-level summary and developer-level detail.
- Critical finding validation: experts manually verify high-severity issues
- Architectural risk assessment: identify systemic security weaknesses beyond individual bugs
- Compliance mapping: map findings to regulatory requirements (PCI DSS, SOC 2, GDPR)
- Executive summary: board-ready report with risk scoring and remediation roadmap
- Technical report: developer-facing findings with code locations, severity, and patches
Phase 5: Remediation Support & Ongoing Monitoring (Optional)
Post-assessment support to help your team deploy patches, answer questions, and establish continuous security monitoring.
- Patch deployment support: help your team review, test, and merge Shield-generated patches
- Developer Q&A: answer questions about findings and remediation approaches
- Re-scan verification: confirm vulnerabilities are fixed after patch deployment
- Continuous monitoring setup: optional ongoing Shield scans (monthly, quarterly, or on-demand)
- Compliance audit support: assist with security documentation for audits
Manual Code Review vs. SAST Tools vs. Phoenix Shield
Three approaches to codebase security assessment. Here's how they compare on accuracy, speed, and actionability.
Manual Security Code Review
Timeline
4-12 weeks depending on codebase size
Cost
£25K-£100K+ for comprehensive review (security consultants at £1,200-£2,500/day)
Accuracy
High accuracy for context-aware findings, but coverage limited by time and human capacity.
False Positives
Low false positive rate, but slow to verify and prioritize findings across large codebases.
Actionability
Expert-written remediation guidance, but no automated patches. You implement fixes manually.
Best For
High-stakes audits requiring deep domain expertise, complex business logic review, regulatory compliance documentation.
Real Risk
Slow and expensive. Coverage gaps for large codebases. No continuous monitoring. Best combined with automation, not as sole approach.
SAST Tools (Snyk, SonarQube, Checkmarx)
Timeline
Hours to days for initial scan
Cost
£3K-£25K/year for tool licenses (plus internal time to configure, triage, and remediate)
Accuracy
Fast coverage but high false positive rates (30-60% in typical SAST scans).
False Positives
Very high. Teams waste time triaging false positives. Alert fatigue leads to ignored warnings.
Actionability
Identifies issues but provides generic remediation advice. No context for your codebase. Manual fixes required.
Best For
Continuous monitoring in CI/CD pipelines. Developer-facing security checks during development.
Real Risk
False positives create alert fatigue. Generic remediation advice doesn't account for your architecture. Requires dedicated security engineer to manage.
Phoenix Shield
Timeline
1-3 weeks from scan to actionable report with patches
Cost
£10K-£45K one-time assessment (includes AI verification, patches, executive reporting)
Accuracy
Automated scanning with AI verification reduces false positives to under 5%. Human expert review for critical findings.
False Positives
Very low. AI filters false positives automatically. Only verified findings reach you.
Actionability
Auto-generated patches delivered as GitHub PRs. Prioritized by business impact. Immediate action.
Best For
Pre-acquisition due diligence, vendor evaluation, pre-funding security audits, compliance preparation, legacy codebase assessment.
Real Risk
Low. Fast enough for deal timelines. Accurate enough to avoid false alarm fatigue. Actionable enough to fix issues immediately.
Related Solutions
These solutions work well together or complement this offering
Frequently Asked Questions
What is a codebase security assessment?
A codebase security assessment is a comprehensive evaluation that identifies vulnerabilities, security flaws, and risk exposures in software code. It combines automated scanning (SAST, SCA) with manual code review to find issues like SQL injection, cross-site scripting (XSS), authentication flaws, insecure data handling, hardcoded credentials, and dependency vulnerabilities. <a href="/" className="text-phoenix hover:underline">Phoenix AI Company</a> delivers Phoenix Shield, which goes further by using AI to verify findings, eliminate false positives, and generate fixes automatically—delivered as pull requests ready for review.
How long does a security code review take?
Timeline depends on codebase size and complexity. Small applications (under 10,000 lines of code) can be assessed in 1-3 days. Mid-size codebases (10,000-100,000 lines) typically take 1-2 weeks. Enterprise systems with 100,000+ lines may require 3-4 weeks for thorough analysis. Phoenix Shield accelerates this: automated scans run in hours, AI verification happens overnight, and you get prioritized findings with auto-generated patches within days, not weeks.
What vulnerabilities do security assessments find?
Security assessments identify a range of vulnerabilities including: injection flaws (SQL, command, LDAP), broken authentication and session management, cross-site scripting (XSS) and request forgery (CSRF), insecure deserialization, using components with known vulnerabilities (CVEs), insufficient logging and monitoring, hardcoded secrets and API keys, weak cryptography, and insecure API endpoints. Phoenix Shield categorizes findings by severity (Critical, High, Medium, Low) and business impact, so you know what to fix first.
Manual vs automated security reviews - which is better?
Both are necessary. Automated tools (SAST/DAST) provide speed, coverage, and consistency—great for finding common vulnerabilities like SQL injection or outdated dependencies. Manual review provides context, catches business logic flaws, and validates findings. Phoenix Shield combines both: automated engines scan for technical issues, AI verifies findings to reduce false positives, and human experts review critical findings and architectural risks. You get the speed of automation with the accuracy of expert review.
When should you conduct a code security audit?
Key triggers for security audits include: before acquiring a company (technical due diligence), before signing a vendor contract, after a security incident or breach, before a major product launch or funding round, when onboarding a new CTO or security lead, annually as part of compliance (SOC 2, ISO 27001), and when integrating third-party code or open source libraries. Phoenix Shield makes continuous security assessment feasible—run it monthly or on every major release to catch issues early.
How much does Phoenix Shield cost?
Phoenix Shield pricing is based on codebase size and assessment depth. Small projects (under 50,000 lines) start at $10,000 for a full assessment. Mid-market engagements (50,000-250,000 lines) range from $19,000-$45,000. Enterprise assessments (250,000+ lines, multiple repos) are quoted based on scope. All plans include automated scanning, AI-verified findings, auto-generated patches, and executive reporting. Contact us for a custom quote based on your specific needs.
See your codebase through Phoenix Shield
Book a conversation and we'll scan your repo live. No commitment, no sales pitch — just a clear picture of your security posture.
Get a Shield Assessment